How Documentation Reduces OT/IT Risk in Energy Facilities
In energy facilities, documentation is the foundation of safe, reliable operations. Engineering drawings, network diagrams, asset inventories, and system configurations give teams the context they need to understand critical infrastructure. But grids are modernizing, uniting operational technology (OT) and information technology (IT), and creating brand-new vulnerabilities in the wake of progress.
Modern energy environments rely on assets that are constantly being updated, reconfigured, patched, connected to new tools, or integrated with remote access systems. As a result, documentation can quickly become outdated and stop reflecting the real OT/IT environment. This creates operational blind spots, slows incident response, and exposes critical real-world infrastructure to significant cybersecurity risk.
In this guide, we’ll walk through a modern documentation strategy that helps energy companies close critical visibility gaps, reduce OT/IT risk, and operate with greater confidence.
The energy facilities documentation map
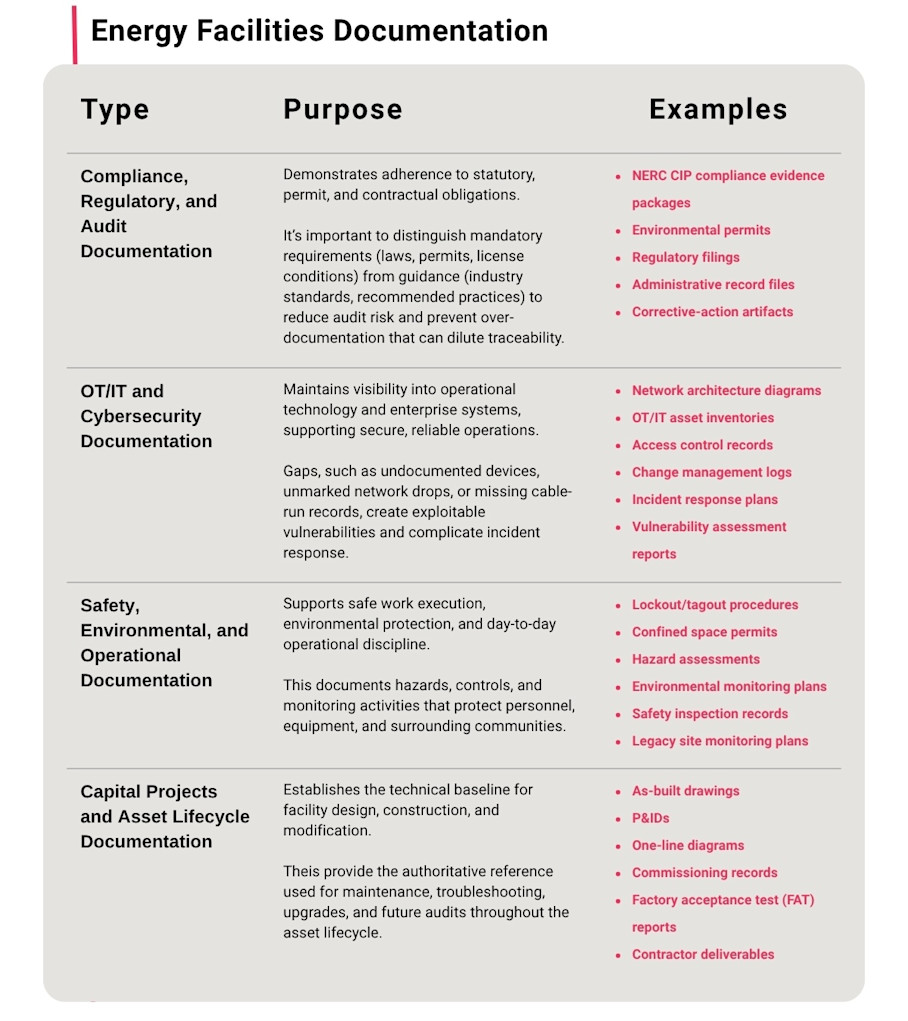
Energy facilities documentation spans several distinct compliance and operational domains. Each carries its own regulatory obligations, documentation types, and consequences for gaps. Knowing what belongs where prevents teams from confusing voluntary best practices with mandatory requirements.
The following table breaks down the core documentation categories, their purpose, and relevant compliance context.
Each domain feeds the others. An inaccurate as-built drawing from a capital project becomes a cybersecurity blind spot when the OT asset inventory doesn't reflect what was actually installed. A missing LOTO procedure becomes an audit finding when it cannot be produced during a spot check.
Why documentation failures expose facilities to OT/IT risk
Most energy facilities were designed in an era when operational technology was isolated. Control systems ran on dedicated networks with no internet connectivity and minimal cybersecurity concerns. As facilities modernize, OT systems are increasingly connected to IT networks to support remote monitoring, data analytics, and operational efficiency.
Legacy control systems that were never designed for network exposure now share infrastructure with internet-connected IT. And the threat is escalating: ransomware attacks against critical infrastructure sectors, including energy, surged 34% in 2025, with 4,701 incidents recorded in the first nine months alone.
In December 2025, a cyber attack compromised OT and industrial control systems across Poland's energy sector, disrupting operator visibility and control across multiple facilities and corrupting firmware on OT devices. State-sponsored attacks, ransomware, and third-party breaches can cause power outages, equipment damage, and serious safety hazards.
Documentation gaps exacerbate these risks. Three failure patterns are especially common:
Asset visibility gaps from outdated as-built drawings: Changes tend to be decentralized. A systems integrator installs a new machine, connects it to the network, and doesn't always fully document the connections. Over time, the network grows with undocumented resources and connections that nobody tracks. When drawings don’t reflect reality, teams cannot identify what’s actually connected to OT networks.
Uncaptured field modifications: Every undocumented cable pull, swapped relay, and temporary vendor laptop represents a device that doesn't appear in any asset inventory. This is sometimes called "Shadow OT": undocumented, unmanaged hardware or software in the OT environment, including unauthorized devices, unapproved software, and forgotten assets like old PLCs or network segments still connected but no longer tracked.
Documentation sprawl: Drawings in SharePoint, photos in emails, PDFs in legacy document management systems, field notes on paper. Many organizations lack a centralized system to manage compliance activities. When evidence isn’t stored in a shared repository, it becomes difficult to track regulatory tasks or verify completion.
These failures translate directly to cybersecurity exposure. Unknown devices on OT networks cannot be patched, monitored, or segmented. Undocumented network drops create uncontrolled pathways between zones. In one substation, OMICRON identified more than 50 persistent connections to external IPs that weren’t documented.
How to build a controlled energy facility documentation system and reduce cybersecurity vulnerabilities
Closing these gaps requires a shift from traditional file organization to a more controlled and accessible system of record. Visual documentation systems provide a single source of truth for energy facilities. By clearly mapping assets, networks, and field connections, they improve operational efficiency, reduce OT/IT risk, and ensure teams have the context they need to manage change safely and maintain audit-ready records.
Here’s how to build one, starting with visual capture and extending through spatial documentation, remote workflows, audit readiness, and lifecycle maintenance.
Visually capture the facility as a single source of truth
Traditional energy facilities documentation relies on flat drawings, disconnected photos, and static PDFs that age the moment they’re created. These formats share a common limitation: they require someone to interpret their connection to the system. A photo of a relay panel doesn't tell you where it sits relative to the OT/IT boundary, for example.
A visual system of record adds a navigable, spatial layer that ties everything together. Energy and industrial facilities increasingly use digital twins for this purpose. These photorealistic, dimensionally accurate 3D models replicate the facility environment in a digital format.
Matterport digital twins are navigable and shareable, offering high levels of facility visibility to all stakeholders:
Remote verification of physical assets: Teams can inspect panel labels, serial numbers, cable runs, and OT/IT zone segmentation from a desk, without entering a live facility.
Consistent capture across sites: Every facility can be scanned using the same process and stored in the same Matterport Cloud, so documentation is consistently managed.
Enterprise-wide visibility: Asset management, compliance, and operational teams all reference the same spatial model rather than maintaining competing versions of reality.
From a cybersecurity standpoint, this means teams can verify that asset inventories match physical conditions, confirm that network segmentation exists where it should, and identify unknown devices before they become attack surfaces. CISA's guidance on OT asset management reinforces that an asset inventory is foundational to designing a defensible architecture. A visual system of record makes that inventory verifiable.
Organize documentation with spatial context
Flat file systems force users to navigate complex hierarchies and siloes to find the document they need, often urgently. Manuals might be in one system, while inspection reports are in another, and work orders in a third. When an auditor or field engineer needs a specific record, the search becomes a scavenger hunt.
Tagging assets inside the digital twin connects documentation to the physical location where it applies. Using Tags and Notes, teams can attach manuals, inspection reports, and work orders directly to the asset in the 3D model. A transformer's maintenance history is pinned to that transformer, not buried in a folder.
Practical benefits include:
Faster retrieval: Instead of searching across multiple systems, teams navigate to the asset in the model and find what’s attached.
Reduced version confusion: One location, one set of current documents. No ambiguity about which revision is authoritative.
Easier audit preparation: When an auditor asks about a specific relay's change history or a panel's access control log, the evidence is organized by location and ready to present.
Tags also integrate with CMMS, BIM, and asset management platforms through Matterport's API/SDK. The Tags Import/Export plug-in keeps tagged data consistent across all twins in a portfolio, preventing the taxonomic drift that creates gaps in multi-site operations.
Linking documentation to exact assets ensures teams always know which devices are installed, how they are connected, and what configurations they use. This visibility prevents OT/IT misconfigurations by making it clear where changes can safely occur. Additionally, Views let administrators control who sees what within a model, supporting controlled access to sensitive infrastructure without sharing entire document repositories.
Enable remote planning and collaboration
Pre-job planning often requires multiple site visits to verify equipment locations and measure clearances. When teams cannot align easily, the risk of OT/IT misconfigurations, untracked changes, and operational errors increases. Visits also expose staff to energized equipment, confined spaces, and other hazards, while planning delays leave critical systems idle or vulnerable.
A digital twin lets the team walk the work virtually before anyone enters the facility. Equipment locations, access routes, LOTO points, and staging areas are all visible and measurable in the 3D model.
Contractors, engineers, and operations teams can annotate and plan workflows using @mention Notes without uncontrolled document sharing. Collaboration stays inside the model rather than scattering across email threads and file shares.
Practical applications include:
Verifying clearances: Confirm adequate space before moving heavy equipment into a turbine hall or relay room.
Planning scaffolding placement: Use Automated Measuring to capture ceiling heights, beam spacing, and obstacle positions directly from the twin.
Sequencing outage work virtually: Ensure that craft crews, engineers, and contractors agree on the execution plan before mobilizing.
Virtual pre-job planning ensures that sensitive OT/IT assets aren’t accidentally modified or exposed during physical work. When a crew knows exactly where the boundary between IT and OT zones falls, the risk of inadvertent operational disruptions drops.
Matterport Cloud provides secure, browser-based access with role controls, so SMEs, auditors, and engineers review only what they’re authorized to see. No VPNs or specialized software required. For critical infrastructure operators, federally compliant clouds with SOC 2 Type II certification and SAML 2.0 SSO are also available, meeting the access control expectations that cybersecurity in the energy sector demands.
Create audit-ready evidence
Audit readiness means that structured, retrievable, time-stamped evidence can be presented on demand. At most energy facilities, it means pulling SMEs from operations, hunting through file shares, and scheduling physical walk-downs weeks in advance.
Strong audit evidence is:
Traceable: Linked to a specific asset, location, and responsible party.
Time-stamped: Shows when conditions were captured or when changes were made.
Version-controlled: Demonstrates which revision is current and what changed.
Independently verifiable: Reviewable by an auditor without requiring the original creator's presence.
Matterport's time-stamped 3D captures provide this kind of defensible record. Instead of dispatching an auditor escort team for a physical walk-down, teams can share a browser link to the digital twin.
Every control implementation under NERC CIP must be verifiable. Centralized repositories for policies, access logs, training records, and change management reports simplify the audit process and support accountability.
With a controlled system of documentation, teams can easily produce evidence against a number of common audit questions. For example:
Question | Digital Twin-Based Evidence |
"Show me the physical access controls for this Electronic Security Perimeter." | Digital twins demonstrate the locations of door hardware, badge readers, and signage, tagged with access control policy documents. |
"Confirm that this BES Cyber Asset matches its documented baseline configuration." | Digital twins provide a view of the asset with tagged serial numbers, firmware version records, and linked CMMS change logs. |
"Demonstrate that network segmentation exists between your IT and OT zones." | Digital twins can be used to navigate cable routes, patch panels, and firewall locations, with network architecture diagrams attached for context. |
"Provide evidence of your last vulnerability assessment for this facility." | Digital twins link vulnerability assessment reports to the assets inside the twin, with time-stamped capture showing conditions at assessment time. |
This approach lets teams locate, package, and present evidence efficiently, without pulling SMEs off the floor or scheduling disruptive walk-downs.
Maintain documentation accuracy throughout the facility lifecycle
A documentation system is only as valuable as its last update. Four events should trigger mandatory recapture:
Post-modification scans: Recapture after any physical or network change to OT/IT systems.
Post-outage documentation: Capture the facility's restored state.
Capital project completion: Scan when new equipment is commissioned. A capture at this stage establishes the security baseline for newly installed assets, confirming that OT/IT boundaries, network connections, and access controls match design specifications before the system goes live.
Contractor turnover: Document conditions at the conclusion of any contracted work. Standardized as-built deliverables, acceptance test records, and digital closeout packages should be contractual requirements.
The practical challenge with lifecycle documentation is that large facilities are expensive and time-consuming to recapture in full. Matterport's Merge Spaces allows teams to scan only the portion that changed and merge it into the existing model. BIM files, CAD exports, and E57 point clouds from those scans give engineering teams vendor-neutral as-built baselines, and the High Density capture mode on the Pro3 camera improves visibility of thin structures like pipes and wiring.
Every capture is time-stamped, creating a verifiable visual history of facility conditions. For site transitions, decommissioning, and long-term surveillance, that history proves what existed, when, and in what condition. From an OT/IT risk standpoint, regularly updated documentation reduces “unknown asset" risk.
With every modification captured and every device visible, configuration drift becomes detectable before it becomes exploitable.
Build a defensible documentation posture for your energy facilities with Matterport
Documentation gaps accumulate gradually, through drawings that aren’t updated after outages, contractor modifications that go unrecorded, and compliance folders that only one person knows how to navigate. Individually, these seem minor. Together, they turn documentation from an active defense against OT/IT risk and audit exposure into a liability.
Consistent capture is the most practical starting point. When every facility has a dimensionally accurate digital twin as its baseline, documentation becomes structured, retrievable, and verifiable by default. Spatial tagging connects records to the physical assets they describe. Secure cloud access lets teams collaborate remotely without uncontrolled file sharing. Standardized exports feed directly into enterprise systems.
Explore Matterport for Utilities teams
